The Business Case for Account Discovery in Entra ID Governance
- Derek Morgan

- 3 days ago
- 6 min read
I've worked with organizations carrying massive application portfolios where app owners can't answer a basic question: who has access to my app right now? The mid-market enterprise runs about 200 SaaS apps (HYCU 2024). Large enterprises average closer to 350 (Productiv 2024).
Simply put:
Everyone carries its own user store, its own admin console, its own version of the access list.
App owners answer the access question with a screenshot from their admin console. Stale accounts accumulate. Contractor accounts persist past their contracts. Service accounts created for one-off integrations stay alive after the integration is gone. Accounts created locally, before SCIM provisioning was wired up, sit outside every governance process the company runs.
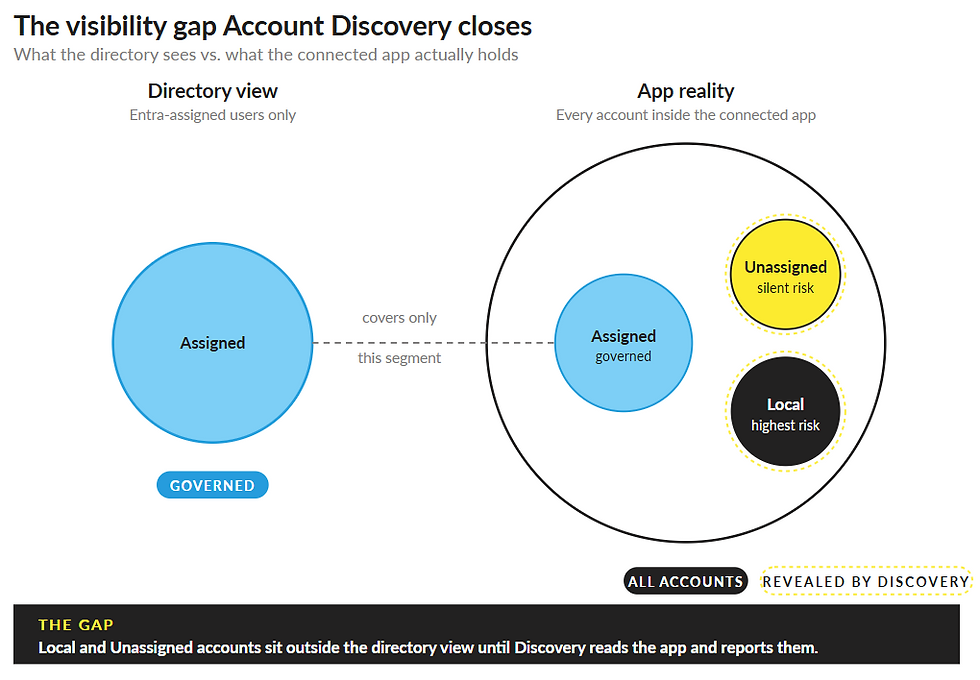
Microsoft Entra ID governs identities in the directory. The directory does not see accounts created locally inside connected apps. That gap is where stale accounts live, where former contractors keep working, where SOX evidence falls apart at audit time.
Fun fact:
Microsoft Secure Access research found 97% of organizations had an identity or access-related incident in the past year, and 22% of those incidents had direct business impact.
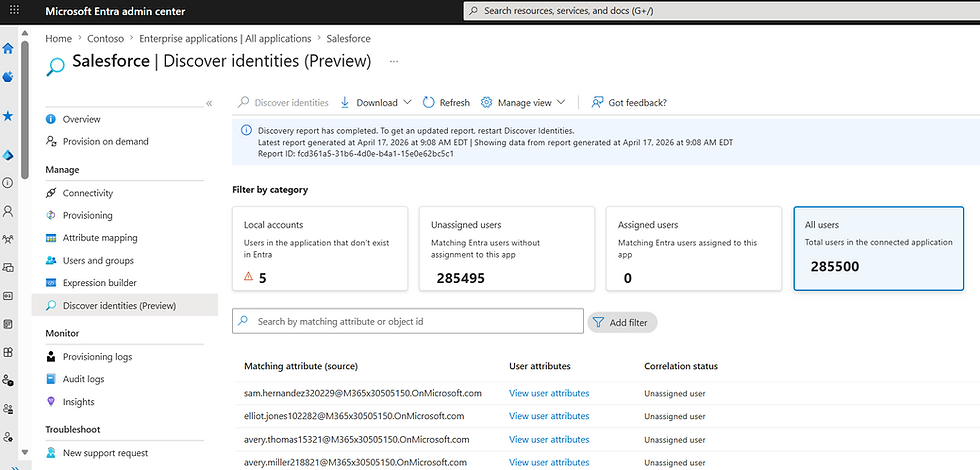
Account Discovery (preview) in Entra ID Governance closes that gap. It reads the connected app, classifies every account it finds, and brings the unknowns into the same governance loop the directory already runs.
Microsoft Learn doc: Discover identities in target applications with Account Discovery (preview) - Microsoft Entra ID | Microsoft Learn
Microsoft blog article: You can’t govern what you can’t see: Closing the identity visibility gap for apps | Microsoft Community Hub
How Account Discovery classifies what it finds
Discovery returns three categories for every account in a connected app.
Local accounts. The account exists in the target app. No matching Entra user. Examples: contractor accounts, service accounts, admin-created direct accounts, accounts that predate SCIM provisioning. The highest-risk category for most clients.
Unassigned users. An Entra user exists. An app account exists. The user is not assigned to the enterprise app in Entra, so the governance loop never reaches them. This is the silent risk category in client environments.
Assigned users. The Entra user exists. The app account exists. The user is assigned to the app. Fully governed.

What this means at design time
For the architect: when you map an existing application to Entra as the identity provider, discovery is the input that tells you what you're inheriting. You can't design the assignment model, the access package scope, or the role mappings without the account inventory the app already holds.
The classification result determines integration sequencing. Apps with a high Local count need a correlation pass before SSO cutover. Apps with a high Unassigned count need an enterprise-app assignment sweep before access reviews can be trusted. Both are predictable work once you have the count.
Configuration mechanics
For the engineer:
License: Microsoft Entra ID Governance add-on, Microsoft Entra Suite, or Microsoft E7.
Roles required: Application Administrator, Cloud Application Administrator, or Hybrid Identity Administrator.
Connector requirements: provisioning must be active, attribute mapping must use direct matching with no expression transforms, and the source connector must support SCIM 2.0 pagination per RFC 7644 Section 3.4.2.4.
Supported at preview: Atlassian Cloud SCIM, Salesforce, SAP Cloud Identity Services, ECMA host connectors, and GitHub Enterprise Cloud (with limitations).
Not yet supported: Workday, SAP SuccessFactors, ServiceNow, AWS, Snowflake. GA is August 2026, with scope expansion on the roadmap (Microsoft 365 Roadmap ID 559476, MC1287372).
What this fixes for the CISO
Three risk surfaces.
Audit exposure. SOX, ISO 27001, SOC 2, and HIPAA controls assume access reviews cover all access. Local accounts inside connected apps are reviewed only if someone in the app team thinks to check. When auditors ask for the access list, the directory export is incomplete by design. Discovery makes those accounts visible to the same review cycle as Entra-governed users, so the directory export becomes the audit answer.
Blast radius of orphaned accounts. A local account in a connected app belonging to a former contractor sits outside lifecycle workflows. It doesn't deactivate when someone leaves. Its credentials don't rotate on a schedule. If compromised, it grants full app access with no Entra signal.
Acquisition and integration cost. Post-merger, the inherited environment carries years of locally-created accounts. Without discovery, the integration team rebuilds an inventory by hand or accepts the gap. With discovery, the inventory comes from the connector itself in a few hours.
ROI framing for the Executive
The cost of an orphaned privileged account is the cost of one breach involving that account. Credential abuse was the #1 initial access vector in the 2025 Verizon DBIR, accounting for 22% of breaches and holding the top spot for the second consecutive year.
Discovery turns a manual reconciliation project, often weeks of consulting time per app, into a recurring automated report. The Entra ID Governance license already paid for Entitlement Management, Access Reviews, and Lifecycle Workflows. Discovery extends those capabilities to accounts the directory couldn't see before. The same license now governs more of the estate.
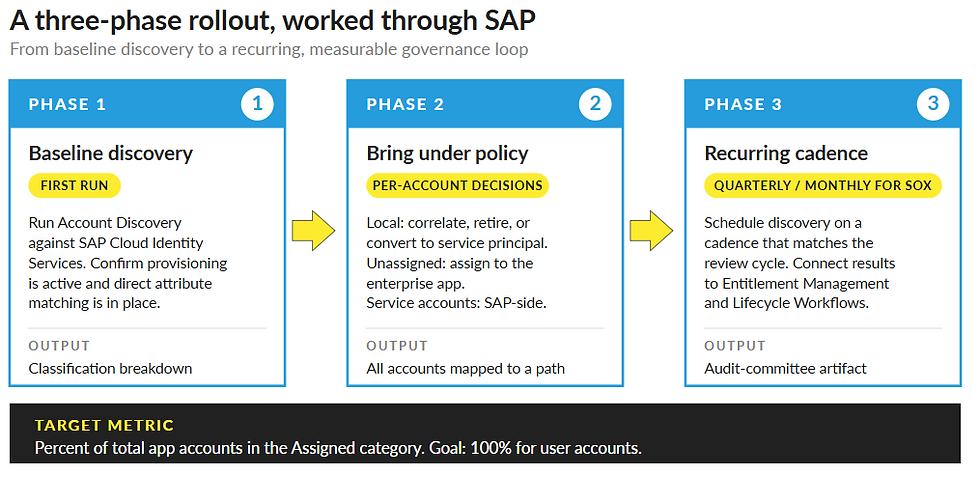
A Three-Phase Rollout, with SAP as the worked example
Why SAP
Most enterprise SAP landscapes are decoupled. S/4HANA, SAP Cloud Identity Services, SuccessFactors, Concur, Ariba, and BTP each carry their own user store. One person ends up with five SAP identities, five sets of credentials, and five separate deprovisioning paths. SAP Cloud Identity Services is supported in the Account Discovery preview, which makes it the highest-yield first target for clients running SAP at scale.
Phase 1: Baseline discovery against SAP Cloud Identity Services
Confirm provisioning is active between Entra and SAP Cloud Identity Services. Confirm attribute mapping uses direct matching with no expression transforms. Run discovery against the SAP Cloud Identity Services enterprise app. Read the classification breakdown.
Expected first-run finding for clients I've worked with: a meaningful share of accounts classify as Local (created directly in SAP) or Unassigned (Entra user exists but never assigned to the SAP enterprise app). Privileged SAP roles sitting in the Local category are the immediate audit conversation.
Phase 2: Bring accounts under policy
For Local accounts: decide per-account whether to correlate to an existing Entra user (using the PowerShell script Assign-CorrelatedUsersWithRules.ps1), retire the account, or convert it to a service principal under Workload Identities governance.
For Unassigned users: assign them to the SAP enterprise app in Entra. This is the fastest cleanup path. No behavior change for the end user. Full governance recovered.
For SAP service accounts and integration accounts (RFC users, technical users, BTP destinations): document them, manage their lifecycle through SAP-side controls, and govern any Entra service principals associated with the integration through Microsoft Entra Workload ID.
For the duplicate-identity problem: correlation rules match the five SAP accounts to a single Entra user, after which the duplicate SAP-side accounts can be retired on a defined timeline.
Phase 3: Make discovery recurring
Schedule discovery on a cadence that matches review cycles. Quarterly works for most environments. Monthly is appropriate for SOX-regulated SAP modules.
Connect results to Entitlement Management access packages. A newly discovered Unassigned user gets pulled into the SAP access package on next review. Connect Lifecycle Workflows. A discovered Local SAP account belonging to a former employee triggers the offboarding flow.
Define the one metric that matters: percentage of total app accounts in the Assigned category. Target 100% for user accounts. Service accounts come out of the user-account metric and into your service-account inventory, with a separate review process.
The same metric is the audit committee report-out. A quarterly chart showing the Assigned percentage trending toward 100% is the artifact your CISO carries into the audit committee meeting.
What to do this quarter
Clients running SAP with Entra ID Governance should run discovery against SAP Cloud Identity Services this quarter and report the classification breakdown to the audit committee. The first run is the artifact. The breakdown is the conversation.
For architects scoping a new app onto Entra as the identity provider: discovery comes before assignment design. Run it before SSO cutover, plan against it, then assign.
GA is August 2026. Workday, ServiceNow, AWS, and Snowflake are on the roadmap for connector expansion. The preview scope is enough to start work today on the highest-risk apps in most enterprise estates.
The directory is the inventory. Account Discovery makes that statement true for connected apps too.
Do You Know Which Accounts in Your Connected Apps Aren't Governed?
Cloud Harbor Consulting partners with technical leadership teams to turn Account Discovery results into a defensible governance plan across Microsoft Entra ID. Schedule a conversation to run a first-pass discovery against a connected app (e.g., SAP Cloud Identity Services, Salesforce) and identify the Local and Unassigned accounts your access reviews are missing.



Comments